Espionage, arcane knowledge, sometimes just for fun—throughout history, cryptographers have developed increasingly intricate codes and ever-more elegant ways to solve them. Today, with the help of computer algorithms and artificial intelligence, we can crack some of the most stubborn secret codes, yet there still remain mysterious, unbreakable ciphers. Here are 23 enigmatic facts about codes and ciphers.
23. The Gold-Bug
“Cryptography” is the study of codes, how they’re made, and how they’re broken. Though code-creation is as old as writing itself, the term "Cryptograph" wasn’t coined until the 19th century, when Edgar Allan Poe used it in his short story “The Gold-Bug.”
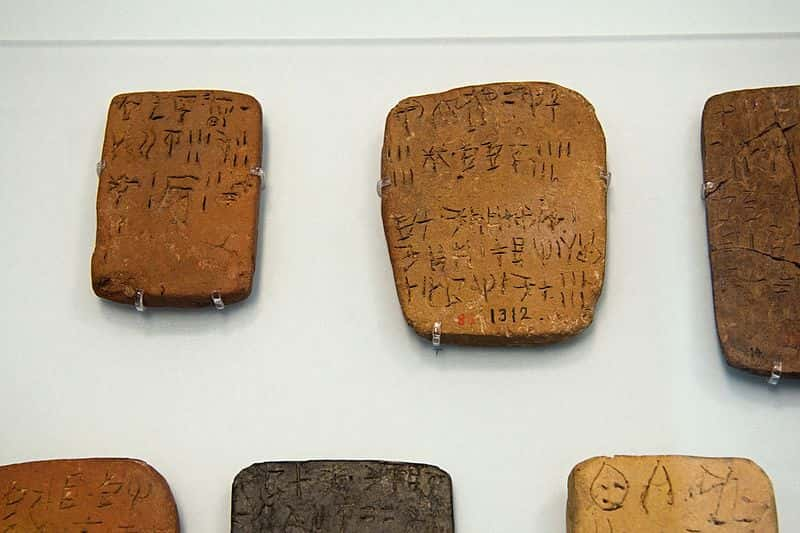
22. “A” Big Mystery
Linear A, the written language of the ancient Crete culture, is found on hundreds of tablets and features hundreds of signs. Some of those symbols reappear in another ancient script, Linear B. But while Linear B has been mostly decoded (and originates from Linear A), Linear A appears to be a completely independent language with no direct ancestors. Deciphering Linear A might tell us not just about the mysterious ancient Cretans, but about how our own alphabet evolved.
21. Ongoing Disk-ussions
The Phaitos Disk, a clay disk that dates back to the Bronze Age, features symbols that resemble those of Linear A, and some symbols that resemble those of Linear B. Solving the Phaitos Disk would be a huge deal, and many people have come forward claiming to have finally deciphered the script—but no explanation has gained wide acceptance.
20. Down in the Valley
The Indus Script, we presume, was a writing system developed in the Indus Valley as early as 3500 BC. It consisted of some 417 distinct symbols. Unfortunately, the Indus Script has only been found in very short messages, making it very, very hard to decipher.
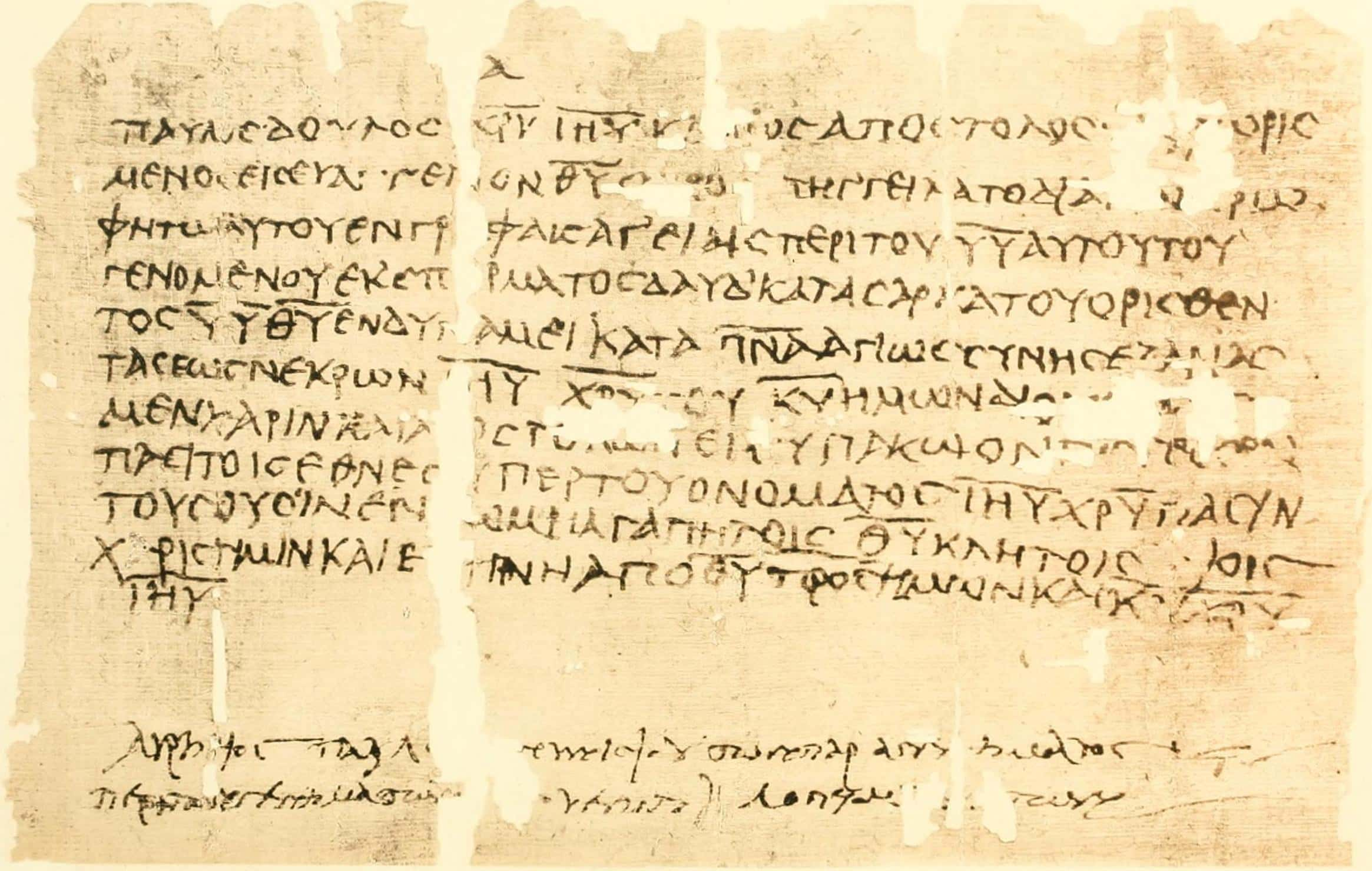
19. Papyrus Oxyrhyncus 90
The content of Papyrus Oxyrhyncus 90 is straightforward, even mundane: It’s just a receipt for some grain. But at the bottom are two lines, made up of ancient Greek letters, that appear to be total gibberish. Researchers have been trying to make sense of it for more than a century.
18. Rongorongo
As mysterious as the massive stone heads that gaze starward from Easter Island is “rongorongo,” the writing system left behind by the Rapa Nui people. With a script that alternates left-to-right and right-to-left across the page, rongorongo has yet to be deciphered, but historians hope it will help them discover more about this mysterious culture.
17. Vinča
A set of more than 5,000 symbols used in Central and Southeastern Europe may be the oldest writing system. The symbols appear in brief notes and date to the Neolithic Era. Like the Indus Valley script, the brevity of the notes makes it impossible to translate, and they may not constitute language at all.
16. Just Google It!
One of the most famous—and most mysterious—medieval manuscripts, the Voynich Manuscript has puzzled scholars for centuries with its strange drawings and indecipherable script. With the help of artificial intelligence, researches are only just starting to chip away at this enigmatic text. In 2018, Canadian researchers were able to possibly translate a sentence of the book using an algorithm and, seriously, Google Translate.
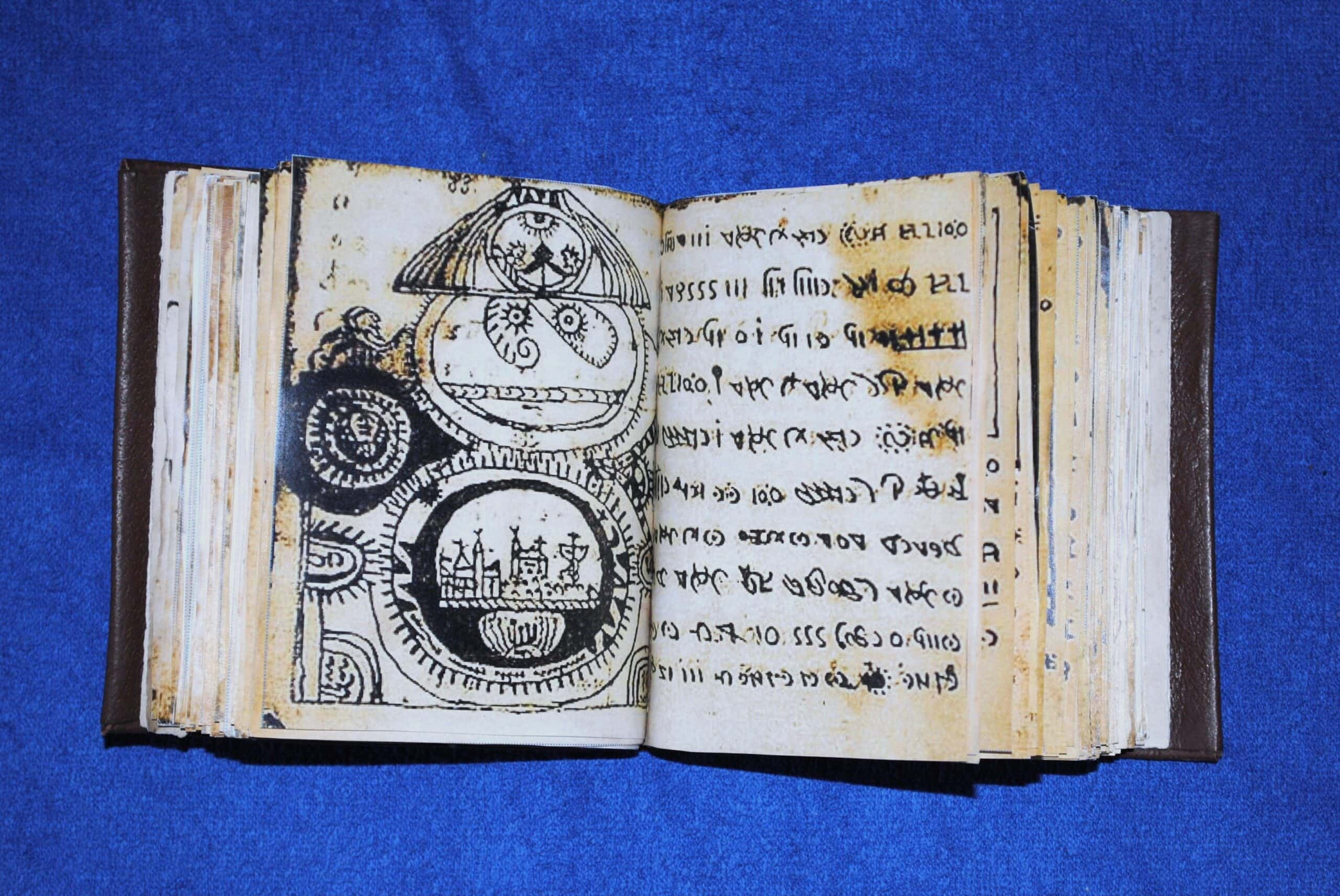
15. The Rohonc Codex
Not as famous as the Voynich Manuscript, but equally mysterious, is the Rohonc Codex. Since its discovery in the 19th century, most scholars have dismissed it as a hoax; that doesn’t make its 792-symbol alphabet any easier to decode.

History's most fascinating stories and darkest secrets, delivered to your inbox daily.
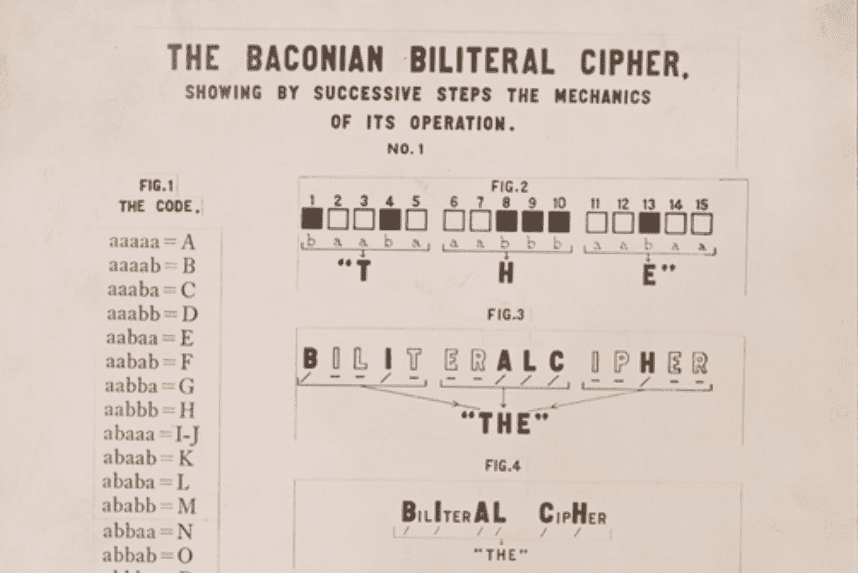
14. That Is the Question
Francis Bacon devised a complex writing system that relied on binary codes and typefaces, allowing him to hide messages in completely unassuming texts. Some scholars even believe Bacon hid evidence in Shakespeare’s First Folios that he, not Shakespeare, was the true author of the plays.
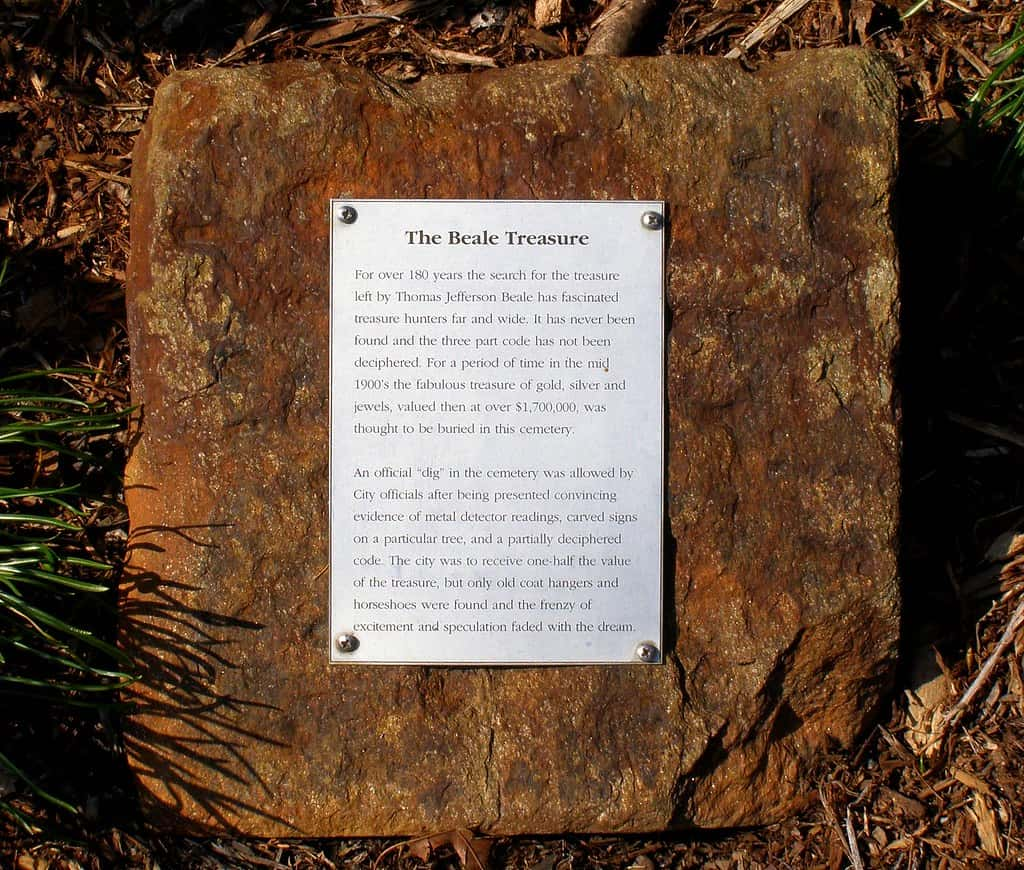
13. Buried Treasures
The Beale Ciphers, published in 1885, were said to reveal a great treasure left by an adventurer, Thomas J. Beale, to his friend Robert Morriss. It’s hard to tell if the Beale Treasure is a hoax or not, or even if the codes are actual solvable codes. That hasn’t stopped treasure hunters from trying.
12. Break It Down
The word "cryptography" comes from the Greek "kryptos," which means "hidden, secret," and the Greek "graphein," or "to write."
11. Oops.
In 1939, cryptologist Alexander D’agapeyeff wrote Codes and Ciphers, a beginners’ handbook to the art of creating and unlocking codes. He included a few “challenge cyphers” in the back to the book to help his readers hone their code-cracking skills. There was just one problem: D’agapeyeff forgot the method he used to create these codes. To this day, no one had been able to translate them, and they were left out of future editions of his book.
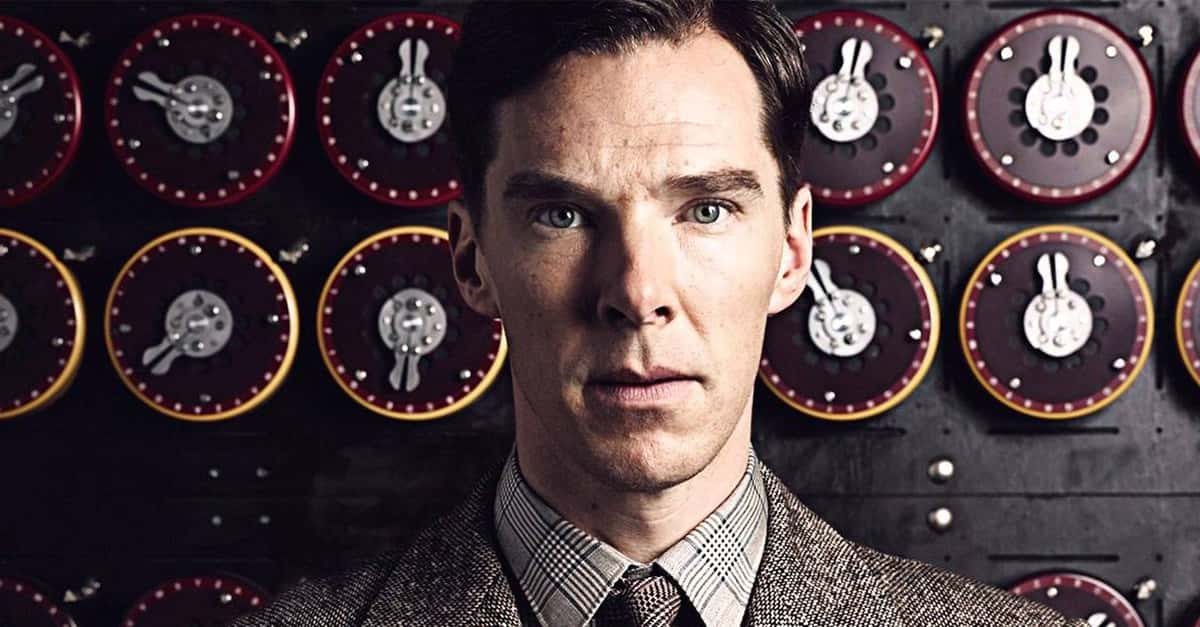
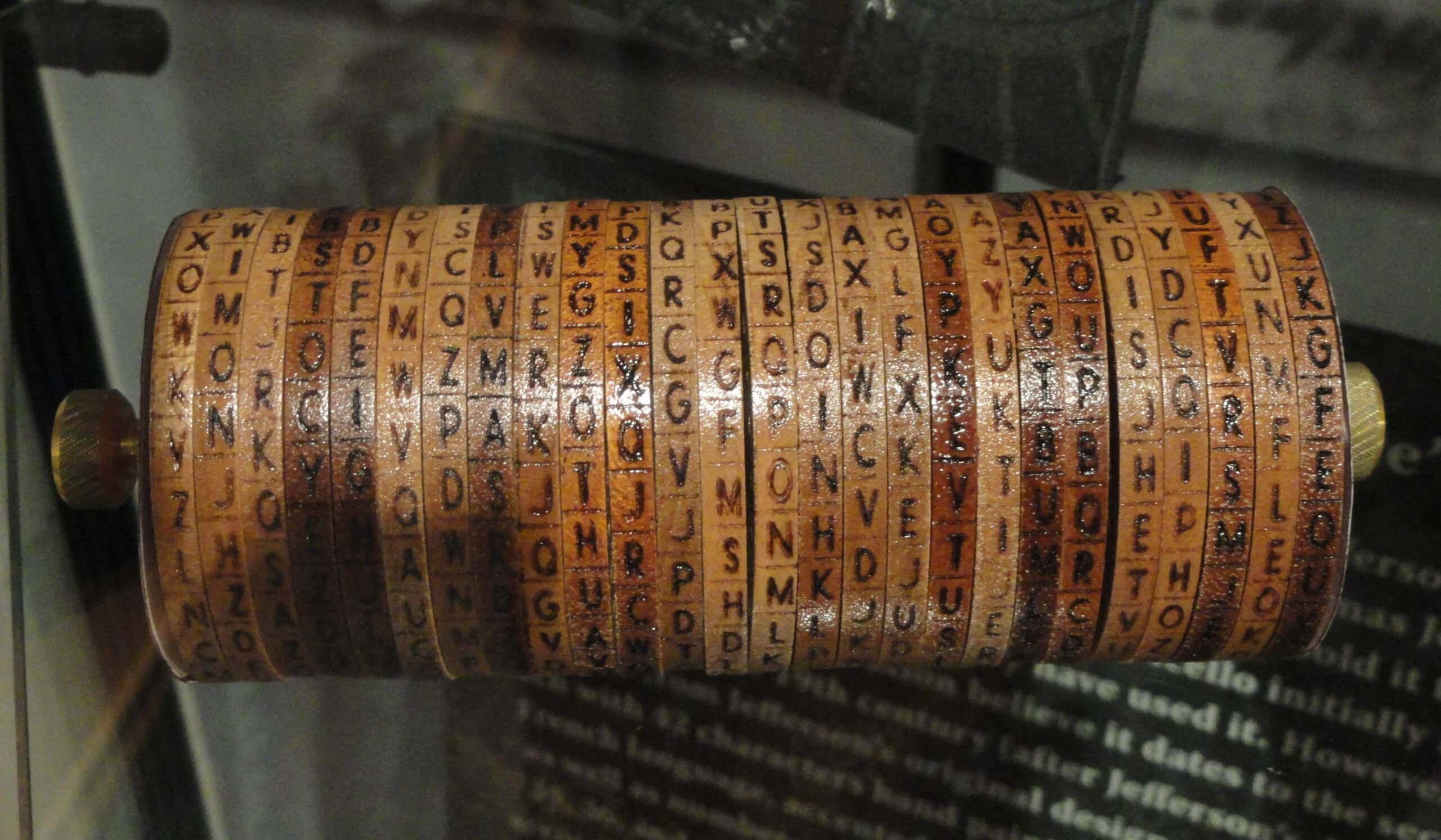
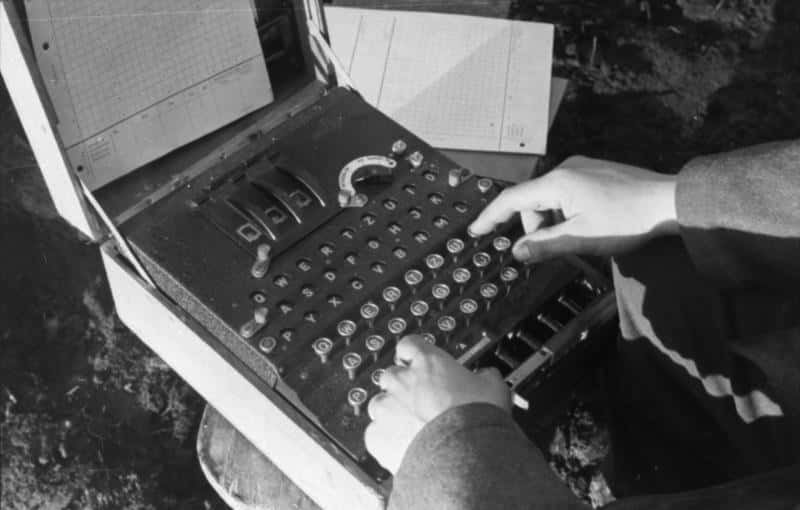
10. Enigmatic
Throughout the Second World War, Axis forces relied on the Enigma Machine, a mechanical coder developed in 1918, to obscure their daily communications. Due to German re-engineering of the machines, these messages were considered undecipherable until 1941, when Alan Turing devised an anti-cyphering machine and a systematic method for code-breaking.
9. The Enigma Code
When he cracked the Enigma code, experts estimate that Alan Turing shortened the war by at least two years. This also meant that cracking the code saved something like 14 million lives.
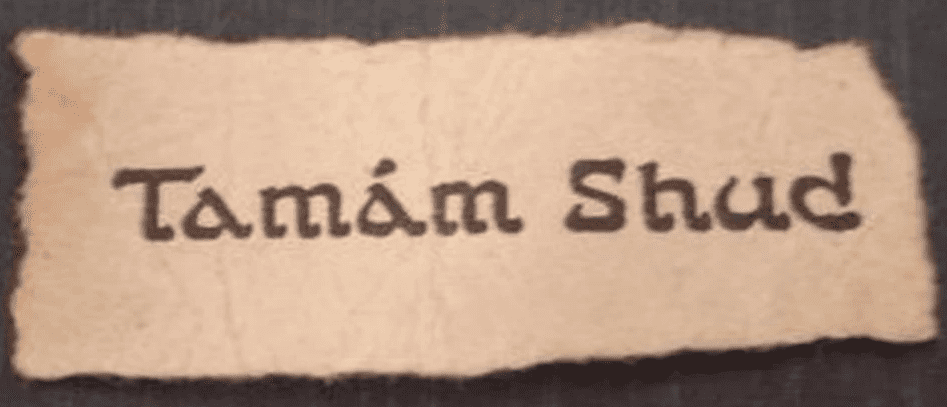
8. Tamam Shud
A man washes up on an Australian beach. He has no identification, no money—his clothes don’t even have tags. The only clue to his identity comes from a scrap of paper containing the words “Tamam Shud,” which mean "ended" or "finished" and came from a Persian book of poems. Miraculously, the book the scrap of paper was taken from is found, but the mystery only deepens: inside the book is an unbreakable code, and the phone number of a young nurse who denied ever seeing the man in her life.
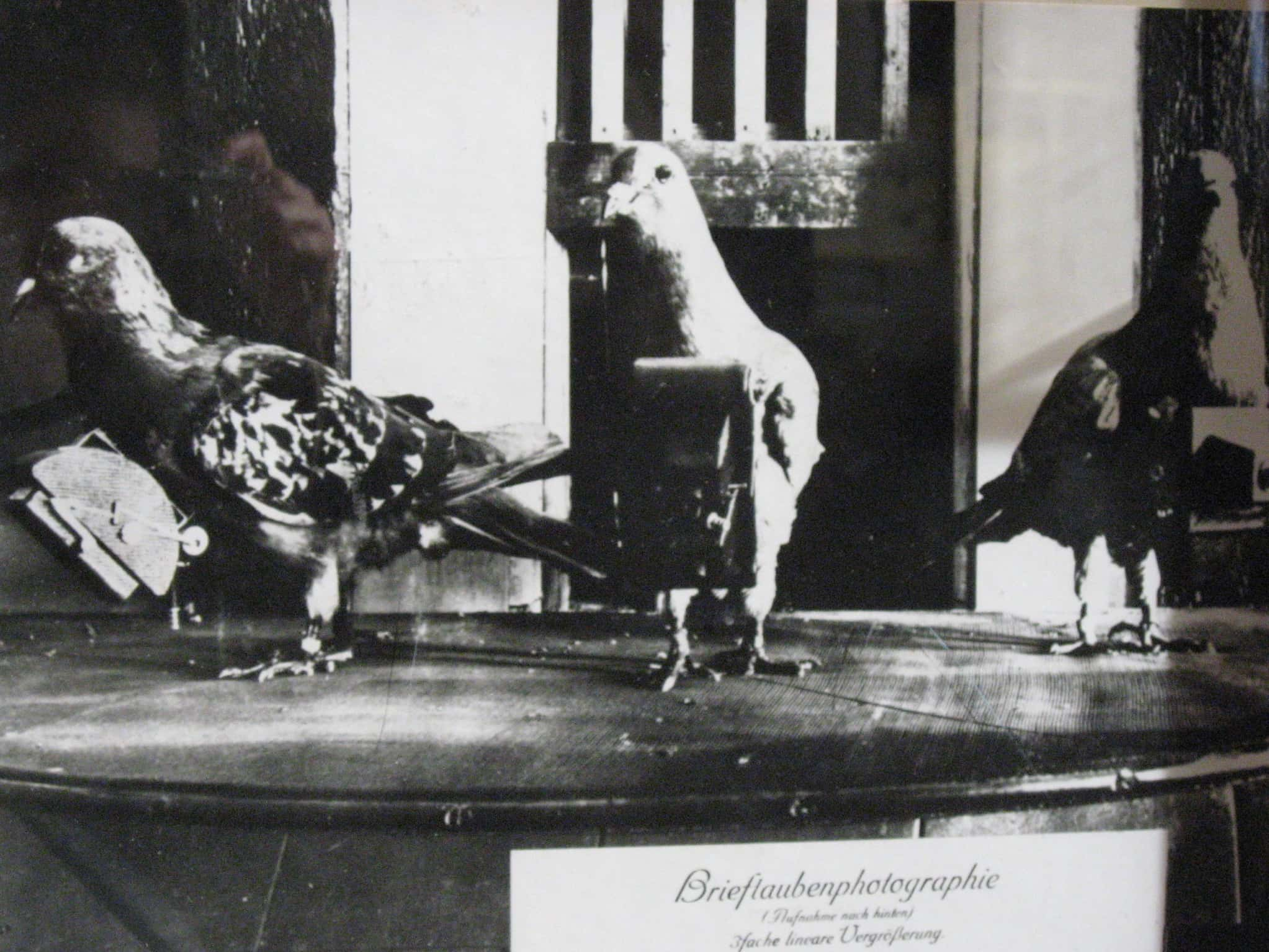
7. The War Correspondent
In 2012, a man in Surrey, UK, was cleaning a chimney when he discovered a dead pigeon. Not an unusual occurrence, except this pigeon had a note attached to his leg. The note, addressed to X02 and signed Sjt. W. Stot, was one of hundreds sent by pigeon during the Second World War. The meaning of this wartime message, however, remains unknown.
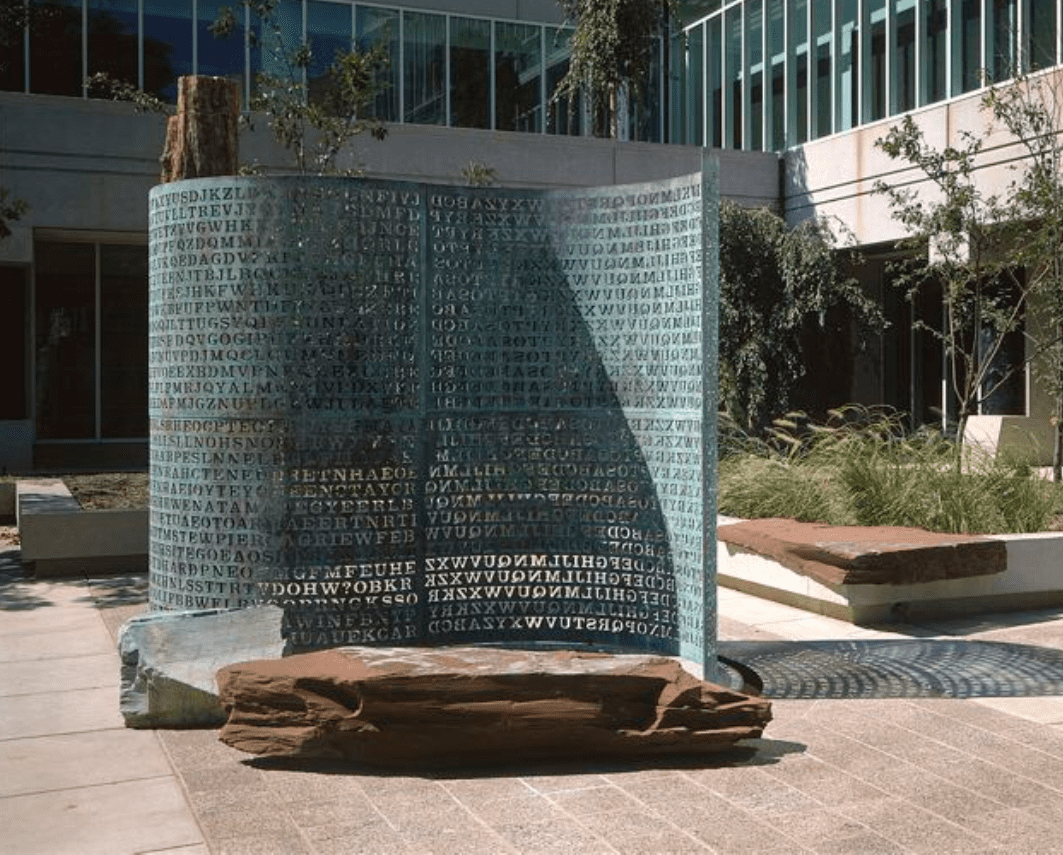
6. Kryptos
A monument to the spies and codebreakers of the CIA, Jim Sanborn’s sculpture “Kryptos” stands outside the CIA offices in Langely, Virginia. With the help of retired CIA agent Ed Scheidt, Sanborn devised four ciphers to be featured in his sculpture. The first three have been solved, but it seems even the CIA can’t make sense of the fourth.
5. The Zodiac Killer
The Zodiac Killer terrorized citizens and taunted detectives in the Bay Area in the late 1960s and 1970s, killing as many as 37 people before disappearing forever. In a flurry of letters sent to newspapers, the killer published a series of codes we presume include information about his true identity. Of the four coded messages sent, only one has been deciphered.
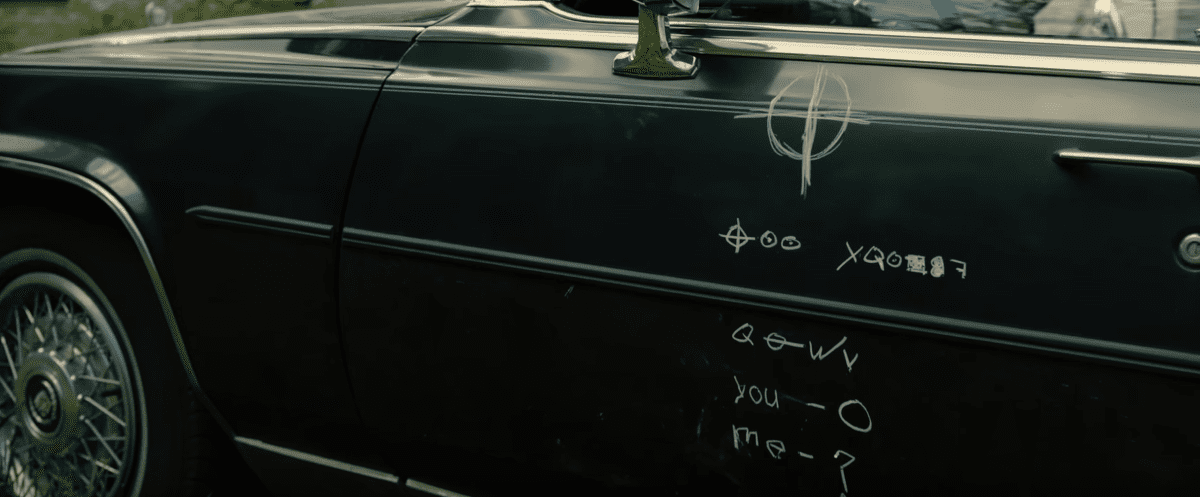 Awakening the Zodiac, Sony Pictures Worldwide Acquisitions
Awakening the Zodiac, Sony Pictures Worldwide Acquisitions
4. The Codes That Stumped a Nobel Laureate
Richard Feynman, a Nobel-prize winning physicist who worked on the Manhattan Project, was given three ciphers by an unknown colleague at the Los Alamos Laboratory. Feynman was able to crack the first one, an excerpt from The Canterbury Tales, but died before he could solve the final two. They remain a challenge to amateur internet cryptographers.
3. Against the Clock
A treasure waits at the Massachusetts Institute of Technology. It's concealed in a lead casket one meter high, and the only way to get it is to crack the 616-letter code that seals the treasure in. Devised by Ron Rivest in celebration of MIT’s 35th anniversary, the code should take 35 years to crack—unless someone can discover a shortcut.
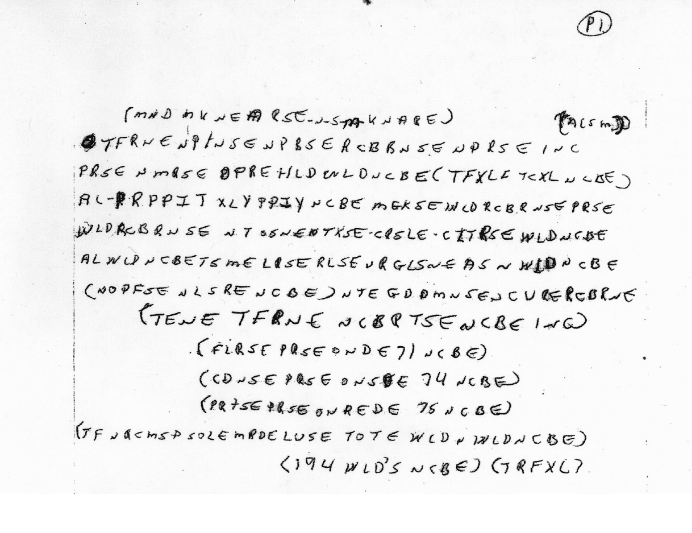
2. Ricky McCormick
In 1999, Ricky McCormick’s body was found in a field near St. Louis, Missouri. He had been missing for three days. The autopsy showed no signs of violence; he simply died and wound up in a field. After 12 years of dead ends, police released two notes found in McCormick’s pockets, a seemingly random jumble of letters police hope will reveal the secret of his death.
1. Sprung a Leak
In 2017, thousands of classified CIA Cyber Intelligence documents were leaked, and they shockingly revealed that CIA hackers focused on codebreaking into smartphones and computers, and worked with British intelligence to try to find a way crack into televisions so as to use them as surveillance devices. WikiLeaks, who published the documents, claim it's "the biggest ever leak of secret CIA documents."
Sources: 1, 2, 3, 4, 5, 6, 7, 8, 9, 10, 11, 12, 13, 14, 15, 16, 17, 18, 19, 20, 21, 22, 23, 24, 25